
David 'Sherlock' Hawkins, co-founder of Abel Danger with Field McConnell, is developing reverse-engineered CSI storyboards for 3-act radio dramas and/or theatre plays to give injured communities a scene-by-scene analysis of high-value-target or mass-casualty events which appear to be associated with the negligent, wilful, reckless or fraudulent use of patented devices to spot fix the times of death and body counts for dead-pool operations on the federal bridge certification authority (FBCA) network, originally implemented on public key infrastructure (PKI) to create, manage, distribute, use, store, and revoke digital certificates on the public-key encryption system invented at GCHQ in the early 70s.

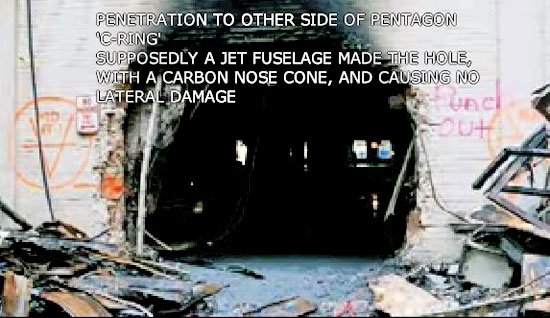
Hawkins is developing template storyboards for radio dramas on the "Patented Dead Pool Bridge" to help selected talk show hosts work through his narrations of events associated with crimes allegedly scripted by Greek Life alumni/alumnae; executed by Serco (the former radio patent monopoly company RCA GB 1929) Con Air SWAT teams and commissioned by agents of Serco's investment banker N M Rothschild & Sons Ltd., including the late Victor Rothschild and the current U.S. Commerce Secretary Wilbur Ross (Greek Life KBΦ Wall Street 19??) who appears to have recruited Lynne Cheney, (Greek Life ΦΒΚ Colorado College 1962), the former director of Lockheed Martin and the former Second Lady of the United States (2001-2009), to script the shoot-down (?) murders of everyone on board Malaysia Airlines Flight 17 (MH17) on 17 July 2014 in East Ukraine when, allegedly, Serco agents switched Con Air/AWACS patented devices from simulation to live fire; spot fixed the time of crash and body counts (298 = Alive from Amsterdam + Dead from Diego Garcia!) and deployed Con Air SWAT teams to the crime scene to remove evidence of a BAE Systems PLC Proximity fuze Priority date 1998-12-23 2004-12-28 US6834591B2 Grant.
Hawkins has evidence of spoliation which suggests that former FBI Director Robert Mueller recruited Con Air SWAT teams through Serco agents in Veterans Affairs and corrupt officials in the State of Illinois for man-in-the-middle attacks over the federal bridge with Jerome Lemelson's Prisoner tracking and warning system and corresponding methods 2000-04-25 US6054928A and that Mueller extorted a Dutch-led joint investigation team (JIT) into concluding that the MH 17 was downed by a Buk surface-to-air missile launched from pro-Russian separatist-controlled territory in Ukraine and conceal the spot fixing use of a British-invented fuze produced by RCA during WWII and manage public perceptions with QinetiQ North America's Social Engineering Protection Appliance 2015-09-01 US9123027B2.
Hawkins also has evidence which suggests Ms. Cheney scripted dead-pool federal-bridge missions for SWAT teams trained by Marine Corps Vets Robert Mueller and Oliver 'Buck' Revell including the murder of up to 50 First Nations prostitutes with biological bullets at a B.C. pig farm witnessed by up to 2,000 subsequently-blackmailed guests; the torture killing of JonBenet Ramsey on Christmas Day 1996; the first live-broadcast mass snuff film in human history on 9/11 and the post-9/11 mailing of anthrax-spore-powder-laced letters to Democratic U.S. Senators (Tom Daschle and Patrick Leahy).
Act 1: Script & Spot; Act 2: Shoot & Snuff; Act 3: Spin & Spoil
Please help Hawkins at https://www.patreon.com/reverseCSIstoryboards with the funds he needs to reach the biggest possible audience for talk-show hosts willing and able to participate in radio dramas intended to expose Serco's and its Rothschild investment bankers' roles on the "Patented Dead Pool Bridge" and develop customized storyboard narrations to help injured communities identify Greek Life scripts and patent-device custodians in re any class-action lawsuits associated with wrongful deaths.
In the interests of transparency, Hawkins gives a list of images or videos which he may use to customize the template poster for a radio drama tentatively entitled "Mueller Vets on Illinois Bridge With MH Spot Fixed Fuze".
Reverse CSI 19 images

Note DOJ (Mueller), Vets and Illinois appear to have set up NL MoD and UK MoD as patsies for spot fixed MH Fuze





Social Engineering


Second Lady Lynne Cheney, Dick Cheney and Condoleezza Rice in PEOC during 9/11.
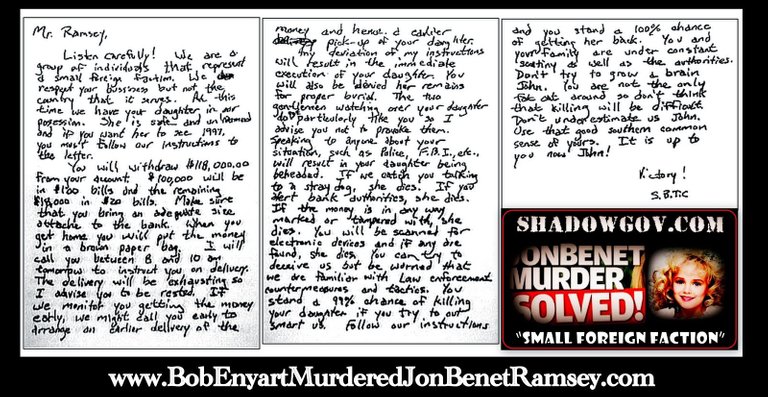
N.B. JonBenet's father given $118,000 bonus by Lockheed Martin directors (Cheney?) apparently for Access Graphic value add of Sun Microsystems to federal bridge.


Reverse CSI 19 – References
"Digital Fires Instructor Serco – [Marine Corps Base!] Camp Pendleton, CA Uses information derived from all military disciplines (e.g., aviation, ground combat, command and control, combat service support, intelligence, and opposing forces) to determine changes in enemy capabilities, vulnerabilities, and probable courses of action."
"Malaysia Airlines Flight 17 (MH17)[a] was a scheduled passenger flight from Amsterdam to Kuala Lumpur that was shot down on 17 July 2014 while flying over eastern Ukraine, killing all 283 passengers and 15 crew on board.[1] Contact with the aircraft, a Boeing 777-200ER, was lost when it was about 50 km (31 mi) from the Ukraine–Russia border and wreckage of the aircraft fell near Hrabove in Donetsk Oblast, Ukraine, 40 km (25 mi) from the border.[2] The shoot-down occurred in the War in Donbass, during the Battle of Shakhtarsk, in an area controlled by pro-Russian rebels.[3] The crash was Malaysia Airlines' second aircraft loss during 2014 after the disappearance of Flight 370 on 8 March.[4]
The responsibility for investigation was delegated to the Dutch Safety Board (DSB) and the Dutch-led joint investigation team (JIT), who concluded that the airliner was downed by a Buk surface-to-air missile launched from pro-Russian separatist-controlled territory in Ukraine.[5][6] According to the JIT, the Buk that was used originated from the 53rd Anti-Aircraft Rocket Brigade of the Russian Federation,[7][8] and had been transported from Russia on the day of the crash, fired from a field in a rebel-controlled area, and the launcher returned to Russia after it was used to shoot down MH17.[9][7][10] On the basis of the JIT's conclusions, the governments of the Netherlands and Australia hold Russia responsible for the deployment of the Buk installation and are taking steps to hold Russia formally accountable.[11]
The DSB and JIT findings confirmed earlier claims by American and German intelligence sources as to the missile type and launch area. In 2014 the US intelligence had also said that Russia had supplied the Buk missile to pro-Russian insurgents, and that the insurgents most plausibly shot down MH17 in error, misidentifying it as a military aircraft.[12][13][14]
Ukrainian Prime Minister Arseniy Yatsenyuk laid the blame on professional soldiers that he said came from Russia, stating that "it wasn't drunken militants with Ukrainian passports [who shot down the Malaysian plane], it was done by Russian professionals and coordinated from Russia”, adding that "the whole world has learned about the Russian lies and Russian propaganda."[15] As of May 2018, the Russian government rejects claims that Russia bears any responsibility for the crash, and denies involvement. The Russian defense ministry said that it had never deployed anti-aircraft missile systems in Ukraine.[8][16] Several false conspiracy theories about the crash have since appeared in Russian media, including that the aircraft was followed by a Ukrainian military jet.[17][13] The Russian Government holds Ukraine responsible since the crash happened in the Ukrainian flight information region.[18][19][20][21]
The Ukrainian Air Force was used extensively in operations against the rebels, and several UAF aircraft had been shot down over the rebel-controlled territory, both before and after the MH17 incident. Immediately after the crash, a post appeared on the VKontakte social media profile attributed to Igor Girkin, leader of the Donbass separatist militia, claiming responsibility for shooting down a Ukrainian An-26 military transporter near Torez.[22] This post was removed later the same day, and the separatists then denied shooting down any aircraft.[23][24][25] In late July 2014, communications intercepts were made public in which, it is claimed, separatists are heard discussing an aircraft that they had downed.[26][27][28][29] A video from the crash site, recorded by the rebels and obtained by News Corp Australia, shows the first rebel soldiers to arrive at the crash site. At first they assumed that the downed aircraft was a Ukrainian military jet, and were dismayed when they started to realise that it was a civilian airliner.[30]"
"BAE Systems PLC Proximity fuze Priority date 1998-12-23 2004-12-28 US6834591B2 Grant
Abstract
A proximity fuze for use in a tube launched projectile carrying a payload, comprising an oscillator for generating a radio frequency signal which has a varying frequency, a single antenna for transmitting the radio frequency signal and for receiving an echo of the radio frequency signal, a first signal processor for generating a range signal corresponding to the time delay between the transmission of the radio frequency signal and the receipt of the echo signal, second signal processor for comparing the range signal with a reference signal and depending on the result of the comparison generating an activation signal for activating the payload, wherein a directional coupler is used for coupling the radio frequency signal from the oscillator to the antenna and to the signal processor and for coupling the echo signal from the antenna to the signal processor, and wherein the second signal processor comprises a threshold detector, a peak detector and a comparator, the threshold detector being for allowing the comparator to utilise the output from the peak detector only once the range signal has reached a predetermined magnitude."
"Inmarsat Global Ltd's Method and apparatus for timing correction in communications systems Priority date 1999-03-05 .. 2009-05-12 US7532891B2 Grant
Abstract
In a wireless communications system, transceivers transmit short bursts to a base station, which determines timing corrections from the time of receipt of the burst and transmits the timing corrections to the respective transceivers. In one aspect, the base station indicates to the transceivers a plurality of time slots, each transceiver selects one of the time slots at random, formats a burst including an indicator of the selected time slot and transmits the burst in that slot. In another aspect, the base station transmits to each transceiver a timing uncertainty value, which determines how the timing correction will be modified by the transceiver as the interval since last receiving a timing correction increases. Data bursts are transmitted in a format comprising a first unique word, a content field and a second unique word, in that order. The bursts are transmitted in a TDMA channel format which can accommodate both short and long bursts in a block format of constant periodicity."
"Serco Awarded New $20 Million Department of Veterans Affairs Contract
October 13, 2010
"RESTON, VIRGINIA – October 14, 2010 – Serco Inc., a provider of professional, technology, and management services to the federal government, announced today that the Company has been awarded a new contract to support the U.S. Department of Veterans Affairs, Veterans Employment Coordination Service (VECS) Veterans’ Reintegration and Retention Program. Serco was competitively selected for this task under the U.S. Office of Personnel Management (OPM), Human Resource Solutions Training and Management Assistance (TMA) Indefinite Delivery, Indefinite Quantity (IDIQ) contract for Human Capital Solutions. The task order is valued at approximately $20 million over a one-year base period.
Under the contract, Serco will provide program management; a knowledge management-based web portal with job hiring tools, e-Learning elements and simulations, videos, and chat rooms; mobile web technologies; a call center; and, career coaching.
This Veterans' program is focused on reintegrating and retaining Veterans within the Department of Veterans Affairs and on providing assessment and hiring tools for all U.S. Veterans returning to civilian life. Serco will build an Assessment Center that will offer an integrated suite of hiring tools that will combine skills, interests, and experience to identify ideal jobs for Veterans looking for new career opportunities. Additionally, Serco will design and deploy a virtual collaboration room where career coaches can work directly with Veterans.
"We are extremely honored to have been selected to support the Department of Veterans Affairs with human capital solutions," said Steve Sieke, Serco's Senior Vice President of the IT and Professional Services Group. This win demonstrates our continued focus on bringing together information technology, human capital management, and structured learning programs.""
"TO: Interim VA Chief of Staff SUBJECT: Administrative Investigation, Conduct Prejudicial to the Government, Veteran Employment Services Office (VESO), Office of Human Resources and Administration (HR&A), Washington, DC (2013-00235 IQ-0004)
Summary
We substantiated that Ms. Mary Santiago, former (retired) Director of VESO, failed to represent VA's Core Values of Integrity, Commitment, Advocacy, Respect, and Excellence (ICARE). We found that Ms. Santiago and Ms. Katherine Nix, a Serco Services, Inc. (Serco) contractor employee, knowingly misrepresented the results of the VA for Vets Veterans Hiring Fair (hiring fair) held in Detroit, MI, June 26–28, 2012, and intentionally reported fictitious results to VA Senior Leadership. Reports produced by Serco, under Ms. Nix's supervision, and approved by Ms. Santiago, reflected that 1,321 tentative selections (defined by Ms. Santiago and Ms. Nix as candidates selected to fill positions) were made during the hiring fair; however, we found that at least 574 or about 43 percent of those reported tentative selections never occurred. Evidence also reflected a high probability that the total number of falsely reported selections exceeded 574. We also found that Ms. Santiago did not properly manage her workforce, frequently used obscene and demeaning language, engaged in verbally abusive behavior toward VESO staff and VA contractor employees, and she engaged in the appearance of a conflict of interest by maintaining a less-than-arm's-length relationship with Ms. Nix. Further, we found that Ms. Nix displayed a lack of candor while testifying under oath. Ms. Santiago announced her retirement shortly after being told of our investigation and declined to be interviewed."
"Serco farewell to NPL after 19 years of innovation
Published: 8 Jan 2015
Serco said goodbye to the National Physical Laboratory (NPL) at the end of December 2014 after 19 years of extraordinary innovation and science that has seen the establishment build a world-leading reputation and deliver billions of pounds of benefit for the UK economy. During that period under Serco's management and leadership, NPL has delivered an extraordinary variety and breadth of accomplishments for the UK's economy and industry. Some of the key achievements during that time have been: – NPL's caesium fountain atomic clock is accurate to 1 second in 158 million years and NPL is playing a key role in introducing rigour to high frequency trading in the City through NPLTime."
"Spot-fixing refers to illegal activity in a sport in which a specific aspect of a game, unrelated to the final result but upon which a betting market exists, is fixed in an attempt to ensure a certain result in a proposition bet; examples include something as minor as timing a no ball or wide delivery in cricket, or timing the first throw-in or corner in association football.
Spot-fixing attempts to defraud bookmakers by a player taking a pre-arranged action to fix the result of that specific event.[1] Spot-fixing differs from match fixing, in which the final result of a match is fixed; or point shaving, in which corrupt players (or officials) attempt to limit the margin of victory of the favoured team. Spot-fixing is more difficult to detect than match fixing or point shaving, and by its nature can be perpetrated by a lone fraudulent player without needing any other players or officials to co-operate. The growth of Internet gambling and increased variety of betting options (e.g. spread betting, first-scorer betting) resulted in the emergence of spot-fixing, particularly through the first decade of the 2000s.[2]"
"Serco Awarded $95 Million Patent Classification Contract with the U.S. Patent and Trademark Office
November 30, 2015
RESTON, VA – November 30, 2015 – Serco Inc., a provider of professional, technology, and management services, announced today the Company has been awarded a patent classification services contract with the United States Patent and Trademark Office (USPTO). Serco will provide initial patent classification and reclassification services to support USPTO's core mission of examining, granting, and disseminating patents and trademarks. The recompete contract has a one-year base period with four one-year option periods, and is valued at $95 million over the five-year period, if all options and award terms are exercised."
"Lynne Ann Cheney (/ˈtʃeɪni/; née Vincent; born August 14, 1941) is an American author, scholar, and former talk-show host. She is the wife of the 46th Vice President of the United States, Dick Cheney and served as the Second Lady of the United States from 2001 to 2009. .. In an interview that took place on October 27, 2006 with Wolf Blitzer on CNN's The Situation Room, Cheney denied that Sisters contained rape or graphic depictions of lesbian sex."
"Shortly Before 12:30 p.m.) September 11, 2001: Richard Clarke Heads to White House Bunker; Told that Vice President Cheney Keeps Hanging up Clarke Telephone, and Cheney's Wife is Interfering Counterterrorism "tsar" Richard Clarke, who is in the White House Situation Room, is informed that Vice President Dick Cheney wants him to come down to the Presidential Emergency Operations Center (PEOC), located below the East Wing of the White House. Clarke heads down and, after being admitted by Cheney's security detail, enters the PEOC. In addition to the vice president and his wife Lynne Cheney, the PEOC contains National Security Adviser Condoleezza Rice, political adviser Mary Matalin, Cheney's chief of staff I. Lewis "Scooter" Libby,[neo-Bolshevik] deputy White House chief of staff Josh Bolten, and White House counselor Karen Hughes. Clarke can see the White House Situation on a screen. But Army Major Mike Fenzel, who is also in the PEOC, complains to him, "I can't hear the crisis conference [that Clarke has been leading] because Mrs. Cheney keeps turning down the volume on you so she can hear CNN… and the vice president keeps hanging up the open line to you." Clarke later describes that Lynne Cheney is, like her husband, "a right-wing ideologue," and is offering her advice and opinions while in the PEOC. When Clarke asks the vice president if he needs anything, Cheney replies, "The [communications] in this place are terrible." His calls to President Bush keep getting broken off. By the time Clarke heads back upstairs to the Situation Room, it is 12:30 p.m. [CLARKE, 2004, PP. 17-19]
Entity Tags: Richard ("Dick") Cheney, Richard A. Clarke, Mike Fenzel, Lynne Cheney, Condoleezza Rice, Joshua Bolten, Mary Matalin, Karen Hughes, Lewis (“Scooter”) Libby
Timeline Tags: 9/11 Timeline
Category Tags: All Day of 9/11 Events, Dick Cheney, Richard Clarke"
"Kappa Beta Phi lore, as told to initiates of the 1950s, was that it was the second oldest campus or Greek-letter fraternity following Phi Beta Kappa, that it also was founded in 1776, that it was founded as an alternative to Phi Beta Kappa to offer pub conviviality rather than salon discussions, and that its reversed Greek letters were chosen to signify that contrast. A membership card of the University of Michigan Chapter of Kappa Beta Phi for the 1952-53 college year supports this by featuring the phrase "Founded 1776." An image of the Kappa Beta Phi key of that era is printed as background on the membership card and shows in the lower left corner a hand pointing at a stein in the upper right corner, three stars in the upper left corner, and a blank lower right corner. Membership was by invitation and open only to men belonging one of five, social, Greek-letter fraternities of which Psi Upsilon was one. The Michigan chapter's purpose was entirely social and revolved around several parties and picnics per year at which alcoholic drinks were always available. An all-day initiation was held once a year in a secluded farm field and involved excessive drinking.[citation needed]
By the 1930s dozens of chapters were in existence, primarily on college campuses. The society was known for being made up of men with a sense of humor. Many colleges and traditional fraternities fought to abolish Kappa Beta Phi, as it was often characterized as a fraternity solely for drinking and partying while making a mockery of academics and more reputable organizations such as Phi Beta Kappa. The Wall Street Chapter of Kappa Beta Phi was founded in 1929 prior to the stock market crash, and it is the only remaining chapter of the society. The stated purpose of the Wall Street Chapter is to "keep alive the spirit of the 'good old days of 1928–29.'"[1][1][2][3]"
"Serco farewell to NPL after 19 years of innovation
Published: 8 Jan 2015
Serco said goodbye to the National Physical Laboratory (NPL) at the end of December 2014 after 19 years of extraordinary innovation and science that has seen the establishment build a world-leading reputation and deliver billions of pounds of benefit for the UK economy. During that period under Serco's management and leadership, NPL has delivered an extraordinary variety and breadth of accomplishments for the UK's economy and industry. Some of the key achievements during that time have been: - NPL's caesium fountain atomic clock is accurate to 1 second in 158 million years and NPL is playing a key role in introducing rigour to high frequency trading in the City through NPLTime."
""Con-Air" in 1/6 San Diego Union Tribune [news article] From: [email protected] (Glenn Campbell, Las Vegas) Date: Tue, 7 Jan 1997 10:37:42 -0800
Subject: "Con-Air" in 1/6 San Diego Union Tribune [news article]
A correspondent passed this 1/6 article on to us. He adds: "The article in the hard-copy paper has a couple of pictures to go with the story (no pix on-line). One picture shows the shoulder patch on the aircrew uniforms, another shows prisoners lined up about to board a Convair 580. The paint job on the plane looked like INS or maybe US Marshals Service, it was a green stripe with an eagle forward of the door."
From http://www.uniontrib.com/uniontrib/mon/news/news_1n6conair.html
(Password required)
The article is relevant here because of recent discussion of Con-Air flights using the “Janet” company name.
…..
In the Disney film, Nicolas Cage plays a hapless prisoner who wanders into a hijack plot aboard a Marshals Service plane carrying a group of high-security inmates.
The Hollywood marshals rough up some of the prisoners, and the plane crashes, leaving the real Marshals Service frowning on the silver screen’s invention, said Kristine Marcy, a top official in charge of detentions.
"We don't beat up our prisoners, and our planes certainly don't crash," Marcy said on a recent trip to San Diego, where she was trying to find more jail space for federal prisoners.
……
Marcy said the air transportation system inspires a high level of commitment in its personnel.
"People are always willing to be on standby or to work overtime," she said, noting that the planes are not always used for prisoner transport.
After a hurricane flattened parts of the Virgin Islands last year, the prisoner transportation system flew in some of the first reinforcements to help establish law and order, she said.
After the Oklahoma City bombing, the airline flew evidence to the FBI crime laboratory [Quantico] in Washington, D.C., she said."
"Jerome H. Lemelson's Prisoner tracking and warning system and corresponding methods US6054928A
A system and method for tracking, monitoring and learning prisoner or parolee behavior involves obtaining prisoner or parolee data and monitoring data for at least one individual prisoner or parolee, storing the prisoner or parolee data and monitored data into a database, learning prisoner or parolee behavior from the prisoner or parolee data and the monitored data in the database, and updating the prisoner or parolee data and the monitored data in the database. Expert system (i.e. including but not limited to fuzzy logic, reinforcement learning, neural networks, artificial intelligence, etc.) algorithms are executed for determining and analyzing deviated behavior by the prisoner or parolee. A parole level is assigned to the prisoner or parolee and it is determined whether the prisoner or parolee is to be moved up or down a parole level depending on whether the prisoner or parolee behavior does not constitute or does constitute prisoner or parolee violations. Furthermore, the system tracks, monitors, and learns the behavior of the prisoner or parolee by controlling and regulating the permitted/prohibited locations or sectors, the permitted/prohibited location or sector dwell times, the permitted/prohibited travel routes, the permitted/prohibited travel times that the prisoner or parolee spends at or between various locations."
"Darren Rubin's Biological active bullets, systems, and methods 2015-12-01US9200877B1 Grant
A novel biological active bullet able to be discharged from a firearm, the ammunition essentially comprising a bullet in a cartridge, the bullet associated with/containing at least one biological active substance, along with a method of use of delivering with this bullet at least one biological active substance having at least one biological effect in the target upon impact and penetration, in addition to the bullet wound, and thus, having additional functions and applications than prior art bullets."
"Jerome H. Lemelson's Friend or foe detection system and method and expert system military action advisory system and method 2000-12-26 US6166679A Grant
Abstract
A friend or foe detection system and method is disclosed. Friend or foe warning unit 20 has a geographic locating system, a communication system for communicating with each of the warning units, and a military force detection system for detecting military forces in a combat area and has a signal routing and control circuitry 50 for controlling operations. A number of components, devices, or sub-systems, such as a transmitter/receiver radio 28, an antenna 26, a microphone 30, a speaker 32, a battery 34, a display 36, a microprocessor 38, a memory 40, a camera 56, a radar/lidar input 54, on/off switch 52, a GPS location system 45 that includes a GPS processor 46, a GPS receiver 42, a GPS antenna 44, are coupled to the circuitry 50. Display 36 provides a display to the user of the unit 20 and shows the location of friendly forces as well as unfriendly or unidentified forces in the area. Display 36 displays text messages for the user of the warning unit 20. The microprocessor 38 together with memory 40 provide microprocessor control of the operations of the warning unit 20. The geographic locating system includes GPS processor 46, GPS receiver 42, and GPS antenna 44, and it is used to determine the exact location of the warning unit 20. The unit 20 is able to broadcast and receive military force information, such as location and status (i.e. friendly, unfriendly, unidentified statuses). An expert system military action advisory system and method for advising military troops or personnel of firing decisions is also disclosed. A firing index is determined based on the membership variables, and the firing index is used to help make the firing decisions. The membership variables and the firing index are defined for an expert system or fuzzy logic system, and the expert system or fuzzy logic system helps determine making the firing decisions. The system and method operate by transmitting target and friendly force GPS coordinate information to determine danger. Alternatively, only target coordinates are transmitted with fire danger indices calculated on a distributed basis by individual warning units and transmitted to the source of fire without friendly force location coordinates to assist in making final firing decisions."
"History - National Prisoner Transportation System On August 20, 1985, the U.S. Marshals Service acquired its first Boeing 727 used for prisoner transportation. The Marshals Service operated the National Prisoner Transportation System, one of the largest transporters of prisoners in the world."
"Police conclude search of Starnet [which forfeited its network to IRS and Customs SWAT teams]
CBC News · Posted: Aug 24, 1999 11:26 AM ET | Last Updated: August 24, 1999
Police have wrapped up several days of searching the offices of Starnet Communications in Vancouver. They entered the company offices and homes of some directors on Friday.
Police were looking for evidence of illegal gambling, distributing child pornography, and money laundering.
Since the raid, Starnet officials say police just don't understand their business.
The search warrant details 18 months of police investigation. It traces a network of companies registered in American and Caribbean jurisdictions.
The warrant also identifies Vancouver as the centre of Starnet's operations, even though this is a grey under Canadian law.
Police note that Starnet's revenues grew dramatically in the past two years, from betting and sex shows and from lucrative licensing agreements for its gaming software.
The investigations and pornography from company sites were grounds for Friday's raid and seizure of company materials.
RCMP Constable Peter Thiessen says investigators left Starnet offices yesterday morning. He says, "They spent the better part of three days going through the business. And as a result of that search the investigation is continuing, but no charges have been laid."
Starnet's many investors were spooked by the raid. Share prices dropped almost 70-percent on Friday. However, the company insists the raid had minimal effect on its operation. Stocks rose slightly yesterday after a day of very heavy trading.
In written statements, company CEO Mark Dohlen said the Wall Street Journal calls Starnet the leader in Internet gaming and entertainment. He says companies like his, those on the cutting edge, are often misunderstood.
Yesterday, Starnet announced it will sell off the sex side of its business. It plans to focus more resources on gaming.
The Police investigation is expected to last for several more months."
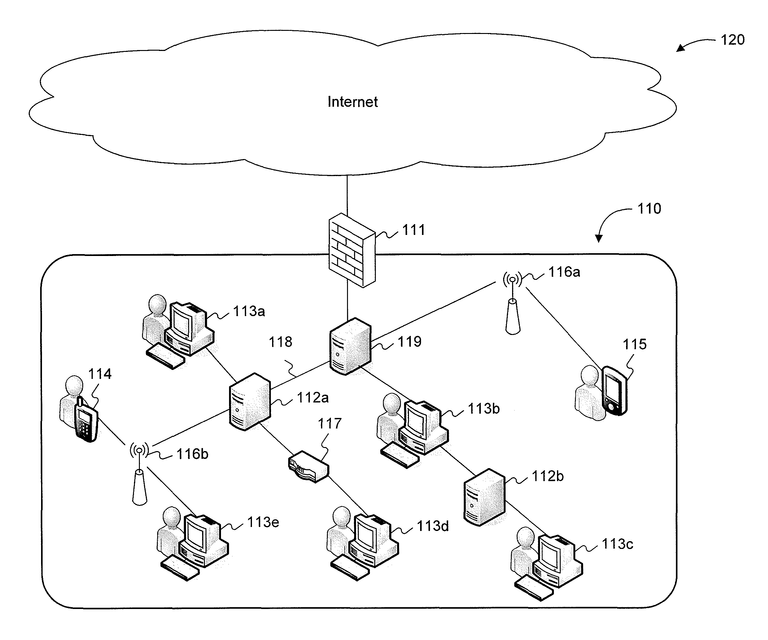
"States Work with Feds for PKI Interoperability
BY: Drew Robb | August 14, 2001
The 1977 epic A Bridge Too Far recaptures one of the most fruitless battles of World War II -- a costly attempt to capture six bridges that connected Holland and Germany. A major gamble from the outset, the campaign led to defeat and more Allied casualties than in the entire Normandy invasion. Fortunately, the folks at the Federal Bridge Certification Authority (FBCA) are having an easier time of it in an initiative aimed at handling some of the thornier questions in government security -- exactly who do you trust when it comes to the handing out and acceptance of digital certificates during e-Government transactions, how do states and federal agencies interoperate to make such certs usable across the government spectrum, and what will it really take to establish "digital" trust to make paperless e-government a reality? The Cast FBCA has gathered an impressive array of federal agencies, states and vendors in an effort to make the initiative a success. On the federal side, there is heavy involvement by the Department of Defense, National Security Agency, General Services Administration, Treasury and the Federal CIOs Council. From the vendor community Entrust Technologies and Baltimore Technologies are directly involved in the FBCA from the technology side, but other PKI/security vendors such as RSA, Cylink, Verisign and Spyrus are also coordinating with the project. At the state level, Illinois is working closely with the FBCA in an interoperability pilot that will probably form the basis of how states share digital certificates with federal and possibly commercial entities. "We are just in the process of developing the cross-certification agreement between FBCA and the State of Illinois CA so we have not tested any applications yet," said Brent Crossland, Deputy CIO for the State of Illinois. "Our timetable is to have the agreement in place by September along with some initial applications." According to Crossland, Washington and New Jersey are also in discussions with the FBCA."
"Nathaniel Mayer Victor Rothschild, 3rd Baron Rothschild, (1910-1990), was a biologist, a cricketer, a wartime officer for the UK Security Service (MI5), a senior executive with Royal Dutch Shell and N M Rothschild & Sons, and an advisor to the UK governments.
Early life
Known throughout his life as Victor, he was the third child and only son of Charles and Rozsika Rothschild. The family home was Tring Park Mansion. He had three sisters, Miriam (1908–2005) who became a distinguished entomologist, Nica (1913–1988), who became a patron of highly influential jazz musicians, and Elizabeth, known as Liberty (1909–1988).
He attended Harrow and Trinity College Cambridge, where he worked in the Zoology Department before gaining a PhD in 1935. At Trinity College, Cambridge, he read Physiology, French and English. While at Cambridge Victor was said to have a playboy lifestyle, enjoying water-skiing in Monaco, driving fast cars, collecting art and rare books and playing cricket for the University and Northamptonshire. Victor married Barbara Hutchinson in 1933, and the couple had three children, Sarah Rothschild (b.1934), Nathaniel Charles (Jacob) Rothschild (b.1936) and Miranda Rothschild (b. 1940). The marriage was later dissolved.
Victor became the third Lord Rothschild in 1937 on the death of his uncle Walter. He sat as a Labour Party peer in the House of Lords, but spoke only twice there during his life (both speeches were in 1946, one about the pasteurization of milk, and another about the situation in Palestine).
Wartime service
During the Second World War Victor worked for the Intelligence Service, and earned the George Medal for his bomb disposal work. In early 1939, he travelled to the United States where he visited the White House to discuss the issue of accepting Jewish refugees from Nazi Germany. In 1939, he was recruited to work for MI5 where he remained for the duration of the War. He was attached to B division, under deputy director Guy Liddell, responsible for counterespionage. In 1940 he produced a series of secret reports on German Espionage Under cover of Commerce and later founded section 'B1c' at Wormwood Scrubs, the wartime home of MI5. This was an 'explosives and sabotage section', and worked on identifying where Britain's war effort was vulnerable to sabotage and counter German sabotage attempts. This included personally dismantling examples of German booby traps and disguised explosives. For this, he was awarded won the George Medal in 1944 for dangerous work in hazardous circumstances. This involved dismantling a pair of German time bombs concealed in boxes of Spanish onions in Northampton. By late 1944, Victor was attached to the 105 Special Counter Intelligence Unit of the SHAEF, a joint operation of MI5 and X2, the counterespionage branch of OSS, a precursor of the CIA, operating in Paris."
"The Office of Strategic Services (OSS) was a wartime intelligence agency of the United States during World War II, and a predecessor of the modern Central Intelligence Agency (CIA). The OSS was formed as an agency of the Joint Chiefs of Staff (JCS)[3] to coordinate espionage activities behind enemy lines for all branches of the United States Armed Forces. Other OSS functions included the use of propaganda, subversion, and post-war planning. On December 14, 2016, the organization was collectively honored with a Congressional Gold Medal.[4]"
"Serco Receives "Supplier of the Year" from Boeing for Enterprise Architecture Expertise
We are extremely honored to receive this recognition for our work in support of Boeing. This prestigious award demonstrates our passion for excellence and ability to apply Serco's Enterprise Architecture expertise across a broad range of applications.
RESTON, VA (PRWEB) MAY 19, 2011
Serco Inc., a provider of professional, technology, and management services to the federal government, has been recognized as Supplier of the Year by The Boeing Company in the Technology category for its state-of-the-practice Enterprise Architecture solutions.
The Boeing Supplier of the Year award is the company's premier supplier honor, presented annually to its top suppliers in recognition of their commitment to excellence and customer satisfaction. This year's 16 winners represent an elite group among more than 17,525 active Boeing suppliers in nearly 52 countries around the world. This selection was based on stringent performance criteria for quality, delivery performance, cost, environmental initiatives, customer service and technical expertise. This is the second time Serco has been recognized as Supplier of the Year by Boeing. In January 2011, Serco also received the Boeing Performance Excellence Gold Award in recognition of the Company's performance excellence.
"We are extremely honored to receive this recognition for our work in support of Boeing. This prestigious award demonstrates our passion for excellence and ability to apply Serco's Enterprise Architecture expertise across a broad range of applications," said Ed Casey, Chairman and CEO of Serco. "We continue to grow our EA practice, and over the past 15 years we have deployed solutions to support enterprises and systems across federal and commercial environments."
"Serco's Enterprise Architecture Center of Excellence is based in Colorado Springs, CO. The team provides a variety of services in support of Boeing's business units as well as research and development efforts. Serco's architecture employs object-oriented (OO)/Unified Modeling Language (UML) to define, design and satisfy defense agencies' mission-critical requirements, including Command, Control, Communications, Computers and Intelligence (C4I). This approach improves system developer's understanding of operational requirements and how best to integrate enterprise operations and systems for the optimal fulfillment of C4I and other operational needs."
"Boeing Co's Intervention flight management system Priority date 1986-08-15 1989-03-07 US4811230A Grant
[Probably installed on a U S Marshals' Con Air Boeing 727 and the Boeing production line after conversation between Kristine Marcy and her brother Field McConnell in December 1988]"
"Southwest Research Institute's (SwRI) Interactive training system for AWACS weapons directors Priority date 1997-10-17 2000-04-25 US6053736A Grant
Abstract
A training system for training AWACS weapons directors. The training system is programmed so that the student can select between a number of different training modes. These include interactive courseware, simulation, and live exercise modes. The system includes a voice recognition unit that is trained to recognize AWACS terminology and to interactively teach them."
"Darren Rubin's Biological active bullets, systems, and methods US9200877B1"
"Airliner irreversible-control anti-hijack system 2005-01-18 US6845302B2 Grant including ATI (automatic/tranquil-Infusion)"
"Howard Lutnick's Real-time interactive wagering on [dead pool] event outcomes CA 2460367 A."
"Boeing Co's Encryption for asymmetric data links Priority date 2001-05-04 US 7023996B2 Grant
Abstract
A method is provided for asymmetrically encrypting data communicated between a ground platform and multiple airborne platforms. The method includes packet encrypting ground-based data so as to preserve routing information while encrypting the remaining data. The packet-encrypted data is then transmitted to the airborne platforms. The method also includes bulk encrypting airborne-based data so as to maximize security. The bulk-encrypted data is then transmitted to the ground platform."
"Vencore Services and Solutions Inc, Cyveillance Inc
Social Engineering Protection Appliance 2015-09-01 US9123027B2 Grant Abstract Methods and systems for detecting social engineering attacks comprise: extracting one or more non-semantic data items from an incoming email; determining whether the one or more non-semantic data items match information stored in a data store of previously collected information; performing behavioral analysis on the one or more non-semantic data items; analyzing semantic data associated with the email to determine whether the non-semantic data matches one or more patterns associated with malicious emails; and based on the determining, performing, and analyzing, identifying the email as potentially malicious or non-malicious. The system also includes processes for collecting relevant information for storage within the data store and processes for harvesting information from detected social engineering attacks for entry into the data store and seeding of the collection processes.
"Motorola Solutions Inc's Dynamic encryption key selection for encrypted radio transmissions 1993-06-22 US5222137A Grant
Abstract
A radio (100) transmits and receives encrypted signals having unencrypted key identifiers, allowing other radios having the corresponding key identifiers and encryption keys to communicate with radio (100). Prior to transmitting an encrypted message, radio (100) selects a unique key identifier automatically and uses the corresponding encryption key to encrypt the message that will be transmitted. Radio (100) transmits the key identifier in an unencrypted format with the encrypted message in order to allow other radios to determine the encryption key used in encrypting the message. When receiving an encrypted message, radio (100) uses the predetermined process stored in the radio (100) to properly select the proper encryption key for use in decrypting the incoming message."
"AWACS Weapons Directors – In a recent exercise, ROADRUNNER '98, several agencies interacted to create several battlespace missions in which "friendly" fighter aircraft and command and control crewmembers participated as trainees, while supporting roles and enemy forces were either played by operational personnel (virtual players) or created by intelligent agent technology (constructed forces)."
"QinetiQ Acquires Cyveillance, Inc. to Strengthen Cyber Security Dominance with Leading Open Source Intelligence Solutions Combined Services Will Offer Comprehensive, Superior Intelligence Solutions to Both Commercial and Government Customers
May 06, 2009 08:57 AM Eastern Daylight Time
ARLINGTON, Va.--(BUSINESS WIRE)--Cyveillance today announced that it has signed an agreement to be acquired by QinetiQ North America, a provider of information technology and engineering solutions to the U.S. government. Under terms of the agreement, pending regulatory approval, Cyveillance will become a QinetiQ North America subsidiary. The company will continue to deliver Internet risk and threat intelligence to commercial organizations worldwide, while providing QinetiQ North America with the technology and expertise to enhance its innovative government-focused Cyber Security and Intelligence solutions."
"Cyveillance launches Cyber Threat Centre
Posted 17 September 2014 · Add Comment
QinetiQ company Cyveillance, has launched its comprehensive cloud-based intelligence platform, the Cyber Threat Centre.
The Centre allows security and risk professionals to undertake their own collection and analysis of online threat intelligence, and to identify and respond to threats faster and more effectively.
The Cyber Threat Centre combines web search, social media monitoring, global intelligence reports, and a suite of investigative tools and databases in an easy-to-use, cloud-based portal. Professionals who are responsible for physical and IT security, incident response, cyber investigations, and online compliance can distill information from thousands of sources outside the firewall into useable intelligence, tailored for their business needs.
"The Cyber Threat Centre is built on our experience from more than 16 years in the cyber security industry," said Cyveillance President Scott Kaine. “It is the natural evolution of our offerings. By taking advantage of the fact that we have already done the work of collecting and tagging vast amounts of data, the Cyber Threat Centre enables security and risk professionals to spend more time on analysis, and less time searching and configuring multiple different portals and data feeds."
The Centre gives organizations access to the same powerful sources, tools and databases already used by Cyveillance analysts, as well as extensive data for cyber investigations and better intelligence. Cyveillance continues to grow its traditional threat analyst practice, which provides tailored, customer-specific threat intelligence to organisations around the world.
"The Cyber Threat Centre is a user-friendly, scalable offering that puts the tools directly in the hands of our global customers and partners," added Sanjay Razdan, Managing Director for QinetiQ New Technologies."
"Serco Receives "Supplier of the Year" from Boeing for Enterprise Architecture Expertise
RESTON, VA (PRWEB) MAY 19, 2011 Serco Inc., a provider of professional, technology, and management services to the federal government, has been recognized as Supplier of the Year by The Boeing Company in the Technology category for its state-of-the-practice Enterprise Architecture solutions. … Serco's Enterprise Architecture Center of Excellence is based in Colorado Springs, CO. The team provides a variety of services in support of Boeing's business units as well as research and development efforts. Serco's architecture employs object-oriented (OO)/Unified Modeling Language (UML) to define, design and satisfy defense agencies' mission-critical requirements, including Command, Control, Communications, Computers and Intelligence (C4I). This approach improves system developer's understanding of operational requirements and how best to integrate enterprise operations and systems for the optimal fulfillment of C4I and other operational needs.
About Serco Inc.: Serco Inc. is a leading provider of professional, technology, and management services focused on the federal government. We advise, design, integrate, and deliver solutions that transform how clients achieve their missions. Our customer-first approach, robust portfolio of services, and global experience enable us to respond with solutions that achieve outcomes with value. Headquartered in Reston, Virginia, Serco Inc. has approximately 11,000 employees, annual revenue of $1.5 billion, and is ranked in the Top 30 of the largest Federal Prime Contractors by Washington Technology. Serco Inc. is a wholly-owned subsidiary of Serco Group plc, a $6.6 billion international business that helps transform government and public services around the world. More information about Serco Inc. can be found at http://www.serco-na.com."
"Serco suffers profits collapse but on 'path to recovery' says CEO Troubled outsourcer
Serco details full extent of its woes and kicks off £555m rights issue
By Alan Tovey, Industry Editor 11:22AM GMT 12 Mar 2015
Troubled outsourcer Serco has launched a £555m rights issue as it starts on what chief executive Rupert Soames called "the path of recovery". Shares in the company, which had more than half a billion pounds wiped off its market value in November when it stunned the market with a huge profit warning, [after fraudulently charging UK government for transporting fake prisoners in Con Air SWAT teams] tumbled again as Mr Soames set out the full extent of the Serco's troubles. … The company's rights issue, on which Rothschild is advising [cf Victor Rothschild, Pearl Harbor and the Henry Tizard Patent Pool, will see 549m new shares issued. The scheme is on a 1:1 basis and is priced at 101p, a deeply discounted 51.1pc compared with the previous closing price, and a 34pc discount on theoretical ex-rights price. The fundraising – which is subject to shareholder approval – is fully underwritten and the proceeds will be used to cut Serco's debt by £450m. At the end of the year Serco's net debt stood at £682m. The company said that subject to the rights issue's completion, it had struck an agreement with its creditors to refinance its funding."
"Serco Inc. Capabilities Chemical, Biological, Radiological, Nuclear and Explosive (CBRNE) SoftwareSupport Develop, demonstrate, implement and transition technologies to improve software/hardware development, fielding and sustainment support for chemical/biological detection and reconnaissance systems, individual and collective protection systems, decontamination systems, and information management systems for the Warfighter and First Responder, Homeland Defense and civil support activities."
"Boeing Begins World Headquarters Operations in Chicago
The Boeing Company began operations on schedule today [Sep 4, 2001] at its new world headquarters building in downtown Chicago.
Approximately 200 employees began unpacking and familiarizing themselves with the building, located on the Chicago River at 100 North Riverside. The company expects approximately 400 employees to be working on the building's top 12 floors by the end of the year.
Boeing and a team of more than 70 subcontractors, vendors and consultants delivered the finished office space, sophisticated telecommunications system, and computing infrastructure on schedule after 117 days of focused, intense effort. The aggressive schedule was driven by the company's commitment to employees with families to coordinate the opening with local school schedules.
Boeing Chairman and CEO Phil Condit - who will officially commemorate the opening of the new Boeing World Headquarters during a ceremony at the building tomorrow - announced in March a broad rearchitecture of the company that included the headquarters relocation. In addition, the leaders of the company's business units were given increased authority and responsibility to run their operations based on the needs of their customers, markets and communities where they do business.
"Boeing is in the midst of many exciting changes, and our new world headquarters in Chicago is part of our ongoing transformation," Condit said. "We intend to grow our enterprise here and create businesses that open frontiers and advance technology, while allowing our business leaders in other locations to drive their businesses to their full potential."
The building is designed with a vision of instant access to information by anyone from anywhere. More than 225 miles of data, communications and security cable were installed to support the more than 300 computers and 500 telephones needed on opening day.
Office spaces have been equipped with more than 3,000 data and telephone connections to support future information technology advancements along with systems needed to meet the goal of wireless connectivity in the future Boeing employees in Chicago are just a mouse click away from any Boeing facility, customer or supplier in 145 countries. Boeing employees, customers and suppliers visiting the new world headquarters will find a number of "mobile desk" touchdown spaces that provide Internet and LAN access, and equipment needed to be productive while away from their home offices."
Posted from my blog with SteemPress : https://www.abeldanger.org/reverse-csi-19-muellers-vets-on-illinois-bridge-wilburs-rothschild-dead-pool-patents-sercos-con-air-awacs-switch-to-mh-spot-fixed-fuze/